Abstract
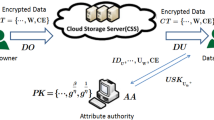
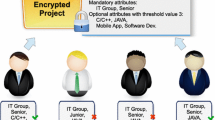
Cryptography-based data distribution is an advanced technique used to control the access of broadcasting data over cloud storage environment. A ciphertext-policy attribute-based encryption (CP-ABE) technique encrypts the data in the cloud scenario, and the data is accessed only when the decryptor satisfies the encrypted access scheme. In this technique, each user is assigned with attributes in the recovering key, and the authorized user is allowed to process the data when their attributes match the keywords embedded in the access policy. Existing techniques used for providing privacy partially hides the access policy in the ciphertext. Therefore, it may leak private information about the user; also, the size of ciphertext is linear with respect to the sum of attributes. In this paper, an efficient privacy sustaining ciphertext-policy attribute-based broadcast encryption technique with AND gate and wildcard access scheme is proposed. The proposed technique provides security proof to sensitive data broadcasted over unsecured channel with hidden access policy. Further, this technique will achieve constant length ciphertext for any number of attributes. Moreover, the communication overhead and the computation complexity are significantly reduced in the proposed method.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
A. Sahai, B. Waters, Fuzzy identity-based encryption, in Eurocrypt 2005, vol. 3494, LNCS, ed. by R. Cramer (Springer, Heidelberg, 2005), pp. 457–473
J. Bethencourt, A. Sahai, B. Waters, Ciphertext-policy attribute-based encryption, in IEEE Symposium on Security and Privacy (IEEE, USA, 2007), pp. 321–334
S. Umamaheswaran, K. Senthil, R. Rajaram, An algorithm for encrypting/decrypting textual messages. JECSE 1(1), 1–10 (2015)
B. Alomair, R. Poovendran, Efficient authentication for mobile and pervasive computing. IEEE Trans. Mob. Comput. 13(3), 469–481 (2014)
V.G. Gopika, A. Neetha, A secure steganographic method for efficient data sharing in public clouds. JECSE 1(2), 11–22 (2015)
M.J.E. Jiju, E. Arun, Cloud computing: characteristics, issues and possible security solutions—a review. JAECE 1(2), 12–23 (2015)
H. Cui, R.H. Deng, J. Lai, X. Yi, S. Nepal, An efficient and expressive ciphertext-policy attribute-based encryption scheme with partially hidden access structures, revisited. J. Comp. Net. 133, 157–165 (2018)
V. Goyal, O. Pandey, A. Sahai, B. Waters, Attribute-based encryption for fine-grained access control of encrypted data, in 13th ACM Conference on Computer and Communications Security (ACM, USA, 2006), pp. 89–98
T.V. Phuong, G. Yang, W. Susilo, Hidden ciphertext policy attribute-based encryption under standard assumptions. IEEE Trans. Inf. Forensics and Secur. 11(1), 35–45 (2016) IEEE
J. Katz, A. Sahai, B. Waters, Predicate encryption supporting disjunctions, polynomial equations, and inner products, in Eurocrypt 2008, vol. 4965, LNCS, ed. by N. Smart (Springer, Heidelberg, 2008), pp. 146–162
J. Herranz, F. Laguillaumie, C. Ràfols, Constant size ciphertexts in threshold attribute-based encryption, in PKC 2010, vol. 6056, LNCS, ed. by P.Q. Nguyen, D. Pointcheval (Springer, Heidelberg, 2010), pp. 19–34
F. Khan, H. Li, L. Zhang, J. Shen, An Expressive Hidden Access Policy CP-ABE, in 2nd IEEE International Conference on Data Science in Cyberspace (IEEE, USA, 2017) pp. 178–186
F. Yundong, W. Xiaoping, W. Jiasheng, Multi-authority attribute-based encryption access control scheme with hidden policy and constant length ciphertext for cloud storage, in 2nd IEEE International Conference on Data Science in Cyberspace (IEEE, USA, 2017), pp. 205–212
K. Emura, A. Miyaji, A. Nomura, K. Omote, M.A. Soshi, A Ciphertext-policy attribute-based encryption scheme with constant ciphertext length, in ISPEC 2009, vol. 5451, LNCS, ed. by F. Bao, H. Li, G. Wang (Springer, Heidelberg, 2009), pp. 13–23
V. Odelu, A.K. Das, Y.S. Rao, S. Kumari, M.K. Khan, K.K. Choo, Pairing-based CP-ABE with constant-size ciphertexts and secret keys for the cloud environment. J. Comput. Stand. Int. 54, 3–9 (2017)
J. Li, Q. Huang, X. Chen, S.S. Chow, D.S. Wong, D. Xie, Multi-authority ciphertext-policy attribute-based encryption with accountability, in 6th ACM Symposium on Information, Computer and Communications Security (ACM, USA, 2011), pp. 386–390
T. Nishide, K. Yoneyama, K. Ohta, Attribute-based encryption with partially hidden encryptor-specified access structures, in ACNS 2008, vol. 5037, LNCS, ed. by S.M. Bellovin, R. Gennaro, A. Keromytis, M. Yung (Springer, Heidelberg, 2008), pp. 111–129
N. Doshi, D. Jinwala, Hidden access structure ciphertext policy attribute based encryption with constant length ciphertext, in ADCONS 2011, vol. 7135, LNCS, ed. by P.S. Thilagam, A.R. Pais, K. Chandrasekaran, N. Balakrishnan (Springer, Heidelberg, 2011), pp. 515–523
G. Ohtake, K. Ogawa, G. Hanaoka, S. Yamada, K. Kasamatsu, T. Yamakawa, H. Imai, Partially wild carded ciphertext-policy attribute-based encryption and its performance evaluation. IEICE 100(9), 1846–1856 (2017)
D. Boneh, C. Gentry, B. Waters, Collusion resistant broadcast encryption with short ciphertexts and private keys, in Crypto 2005, vol. 3621, LNCS, ed. by V. Shoup (Springer, Heidelberg, 2005), pp. 258–275
Y. Vidya, B. Shemimol, Secured friending in proximity based mobile social network. JECSE 1(2), 1–10 (2015)
Z. Zhou, D. Huang, On efficient ciphertext-policy attribute based encryption and broadcast encryption, in 7th ACM Conference on Computer and Communications Security (ACM, USA, 2010), pp. 753–755
J. Kim, W. Susilo, M.H. Au, J. Seberry, Adaptively secure identity-based broadcast encryption with a constant-sized ciphertext. IEEE Trans. Inf. Forensics Secur. 10(3), 679–693 (2015)
Y. Zhang, D. Zheng, X. Chen, J. Li, H. Li, Computationally efficient ciphertext-policy attribute-based encryption with constant-size ciphertexts, in ProvSec 2014, vol. 8782, LNCS, ed. by S.S.M. Chow, J.K. Liu, L.C.K. Hui, S.M. Yiu (Springer, Cham, 2014), pp. 259–273
Z.Y. Jianfeng, J.Z. Cui, Adaptively secure ciphertext-policy attribute-based encryption with dynamic policy updating. J. Sci. 4, 019 (2016)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2019 Springer Nature Singapore Pte Ltd.
About this paper
Cite this paper
Sravan Kumar, G., Sri Krishna, A. (2019). Privacy Sustaining Constant Length Ciphertext-Policy Attribute-Based Broadcast Encryption. In: Wang, J., Reddy, G., Prasad, V., Reddy, V. (eds) Soft Computing and Signal Processing . Advances in Intelligent Systems and Computing, vol 900. Springer, Singapore. https://doi.org/10.1007/978-981-13-3600-3_30
Download citation
DOI: https://doi.org/10.1007/978-981-13-3600-3_30
Published:
Publisher Name: Springer, Singapore
Print ISBN: 978-981-13-3599-0
Online ISBN: 978-981-13-3600-3
eBook Packages: Intelligent Technologies and RoboticsIntelligent Technologies and Robotics (R0)